Understand the Importance of G Router Security Configuration and Setup
Your home network's backbone, your router plays a crucial role in maintaining a secure wireless connection. A properly configured router is essential for a seamless internet experience, fast speeds, and a secure connection. G Router security configuration and setup are critical in preventing unauthorized access, encrypting data, and keeping your network safe from cyber threats.Why is G Router Security Configuration and Setup Necessary?
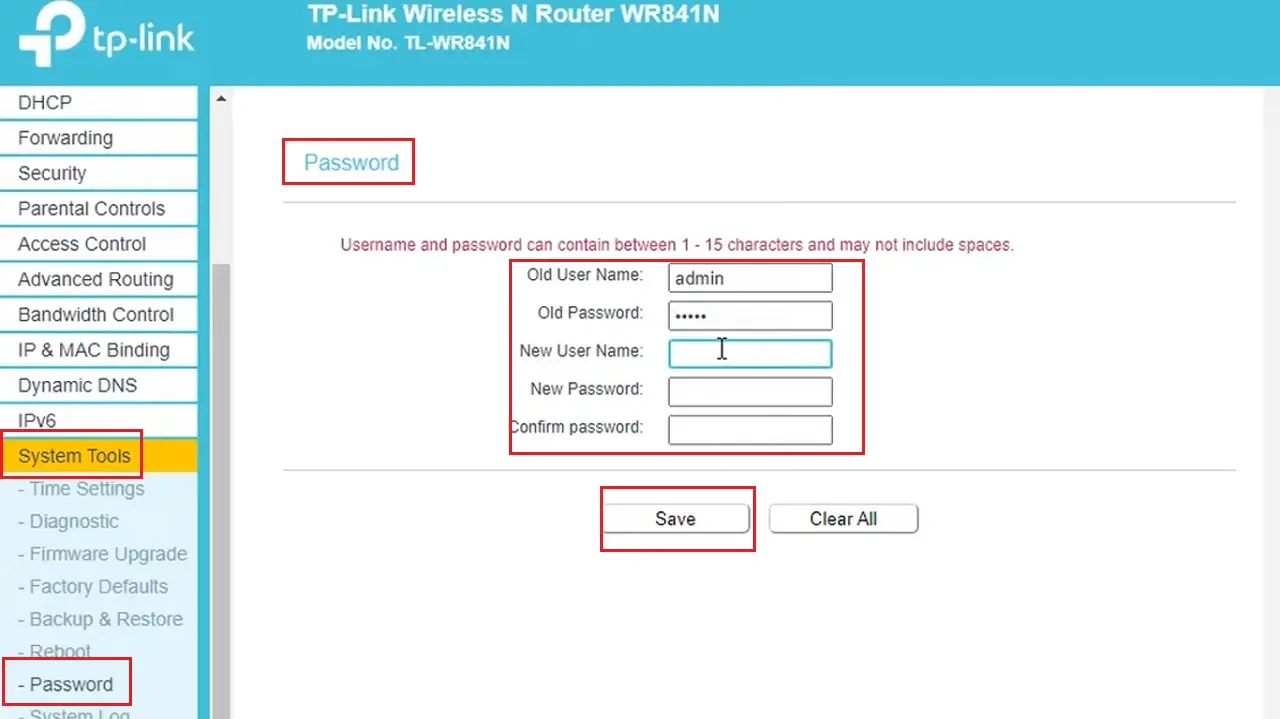
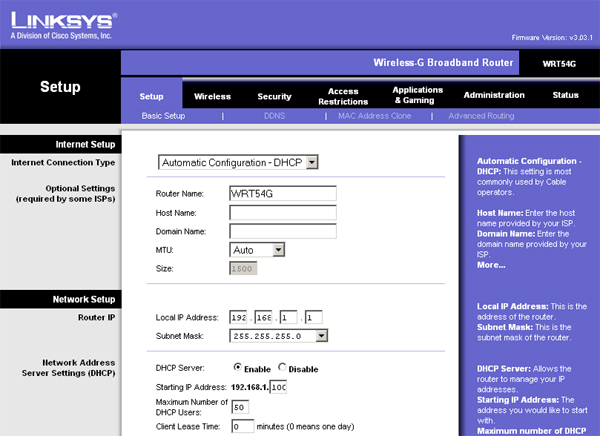
A well-configured router ensures that your network remains secure and prevents unauthorized access to your personal data. Here are some reasons why G Router security configuration and setup are necessary: * Protection against hacking: A poorly configured router leaves your network vulnerable to hacking attempts, allowing cyber attackers to access your sensitive information. * Encryption of data: Proper router configuration ensures that your data is encrypted, making it difficult for hackers to access your sensitive information. * Prevention of malware and viruses: A secure router configuration prevents malware and viruses from entering your network, keeping your devices safe. * Parental control: With a properly configured router, you can set up parental controls, restricting access to certain websites and content. Here are the basic steps for G Router security configuration and setup: * Change the admin password
This particular example perfectly highlights why G Router Security Configuration And Setup is so captivating.
: Changing the default admin password is the first step in securing your router. Use a strong and unique password that is difficult to guess. * Enable WPA2 encryption: WPA2 encryption is a strong security protocol that prevents unauthorized access to your network. * Set up a guest network: A guest network allows you to separate your primary network from your guest network, ensuring that your primary network remains secure. * Configure parental controls: Set up parental controls to restrict access to certain websites and content. * Update firmware regularly: Regularly update your router's firmware to ensure that you have the latest security patches and features.Advanced G Router Security Configuration Options
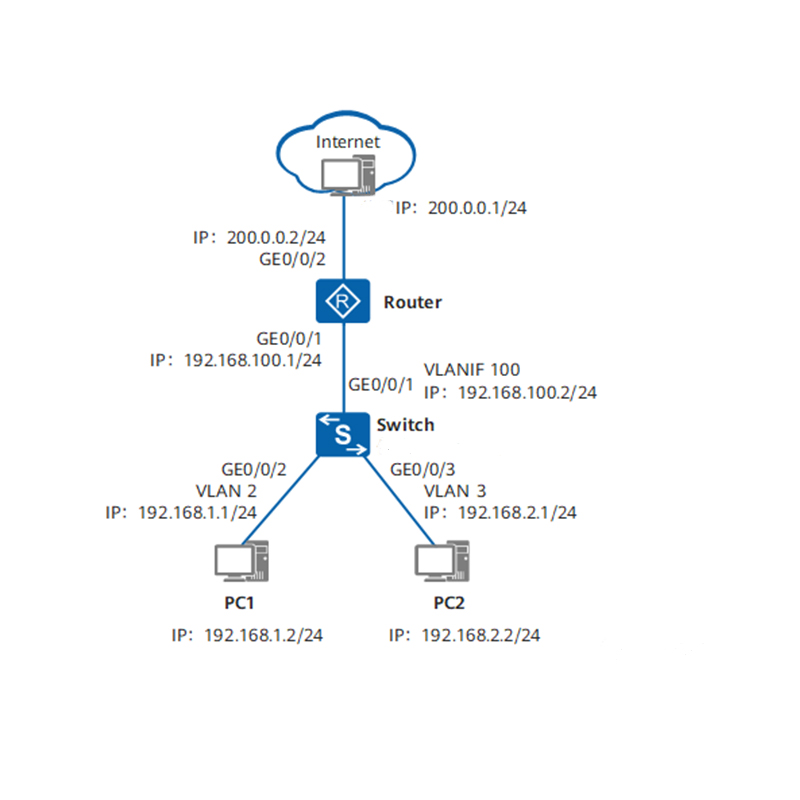
In addition to the basic configuration steps, here are some advanced G Router security configuration options: * Multiple WAN connections: Multi-WAN allows you to connect multiple internet connections at the same time, increasing your network's resilience and speed. * Firewall configuration