Preventing Identity Theft from Public Databases: A Comprehensive Guide
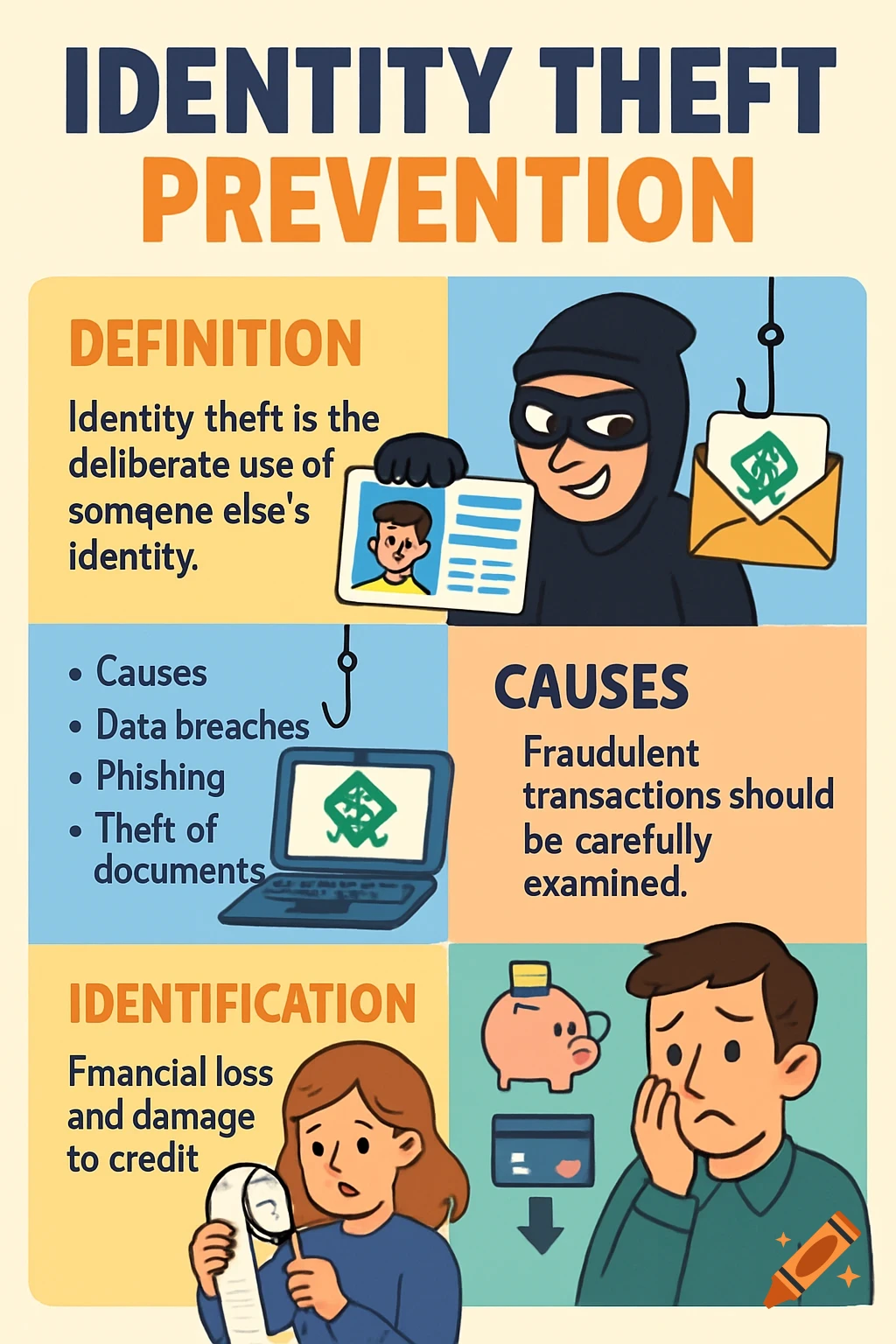
With the increasing number of public databases storing sensitive information, preventing identity theft has become a top priority for individuals and organizations alike. Identity theft can have far-reaching consequences, including financial loss, reputational damage, and legal issues. In this article, we will discuss the importance of preventing identity theft from public databases and provide a comprehensive guide on how to do it.
Identity verification is crucial for safeguarding both individuals and organizations. It helps prevent identity theft, financial loss, reputational damage, and legal issues by ensuring only authorized individuals can access protected resources. Dec 8, 2024
Limiting Online Visibility
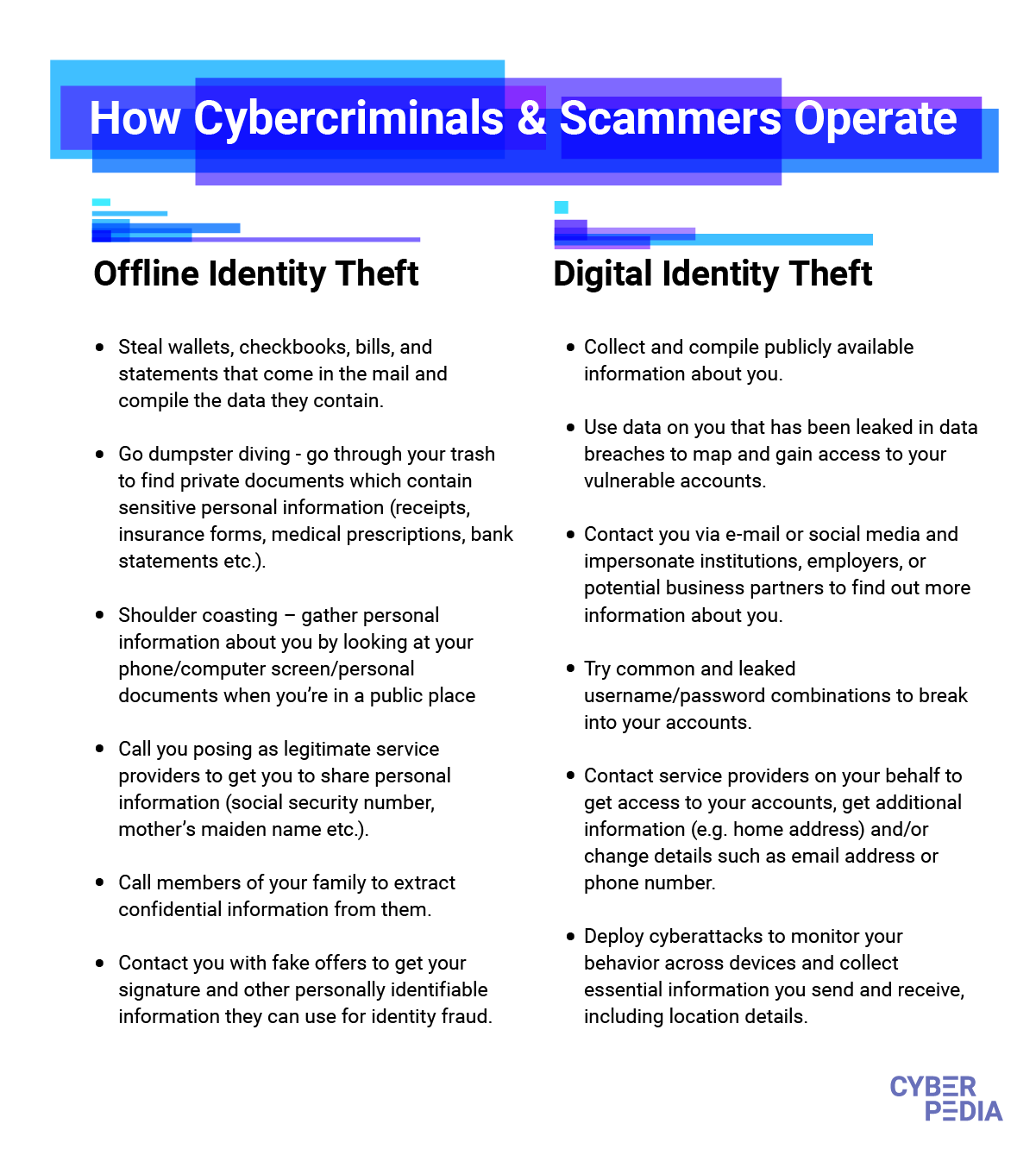
To prevent your private data from being collected and reappearing on data broker sites, you need to reduce your online visibility. This means making yourself (or specific information about you) hard to find. To do this, you often need to start by reviewing your online accounts. Jun 19, 2025
Government Strategies for Identity Theft Prevention Technology

Government strategies for identity theft prevention technology are evolving in response to complex cyber threats and increasing digitization. By adopting comprehensive legal, technological, and educational measures, governments can significantly reduce the risk of identity theft and foster trust in digital services. Sep 1, 2025
Inside the Database: New Face of Identity Theft in Enterprise Environments
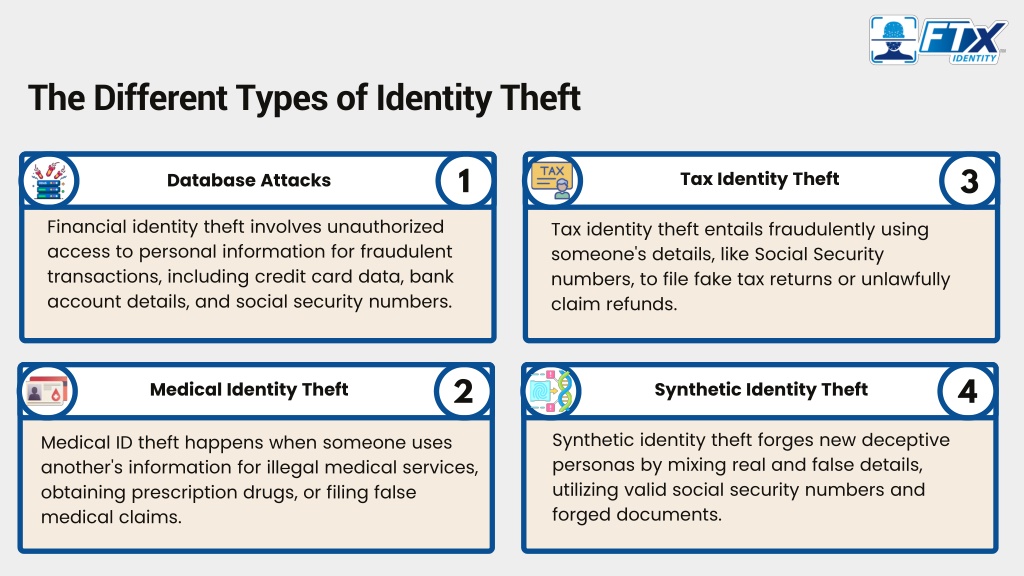
Identity theft in enterprise environments is rarely about a stolen credit card. It's about gaining unauthorized access by assuming the identity of a legitimate user usually through stolen credentials, compromised endpoints, or abuse of overly permissive roles. The New Face of Identity Theft: Inside the Database Identity theft in enterprise environments is rarely about a stolen credit card. It's about gaining unauthorized access by assuming the identity of a legitimate user usually through stolen credentials, compromised endpoints, or abuse of overly permissive roles.
Public agencies' efforts to use biometrics technology to prevent fraud and waste raise a number of concerns. This guidance sets forth best practices for government agencies, both in assessing whether alternatives are available and how to mitigate some of the privacy and equity risks associated with reliance on biometric data.
How to Use This Guide

Such details provide a deeper understanding and appreciation for Preventing Identity Theft From Public Databases.
The Identity Awareness, Protection, and Management (IAPM) Guide is a comprehensive resource to help you protect your privacy and secure your identity data online.
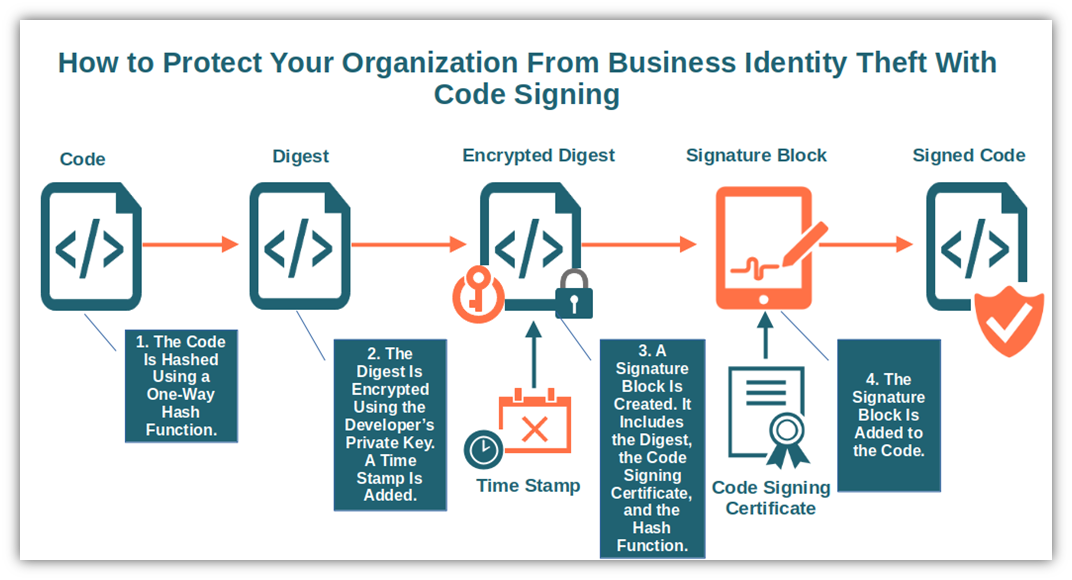
Dealing with Public Databases Storing Sensitive Information
Government databases store vast amounts of sensitive information, including personal details of citizens, classified national security data, and critical infrastructure information. This makes them prime targets for cybercriminals aiming to access, exfiltrate, or exploit such data. The exposure of this information can have far-reaching consequences, from identity theft to national security breaches.
Preventing identity theft from public databases requires a three-pronged approach: data protection, public awareness, and regulation.
- Data Protection: Protect sensitive information by encrypting it, limiting access, and regularly deleting unnecessary data.
- Public Awareness: Educate citizens and organizations about the importance of protecting sensitive information and the risks associated with it.
- Regulation: Establish and enforce regulations to ensure public databases meet rigorous security standards and protect sensitive information.

Additional Tips for Preventing Identity Theft from Public Databases
Here are some additional tips to help prevent identity theft from public databases:
- Be Cautious with Personal Information: Only provide personal information when absolutely necessary, and opt for two-factor authentication whenever possible.
- Monitor Credit Reports: Regularly check credit reports to detect any suspicious activity.
- Use Identity Theft Protection Services: Consider using identity theft protection services to monitor your credit reports, online activity, and public records.
Preventing identity theft from public databases is a complex issue that requires a comprehensive approach. By understanding the risks, taking proactive measures, and staying informed, individuals and organizations can protect sensitive information and prevent identity theft.